Enterprise Identity and Access
Management Services.
We design and implement IAM solutions for organizations that require secure, compliant, and maintainable access control across complex systems

Access Management for your
business sector
We design and implement Access Management (AM) solutions that cover three key areas.

Customer Identity & Access Management: CIAM
Provide identity and access management for millions of customers with a strong focus on user experience, security, and regulatory compliance

Partners Identity & Access Management: PIAM
Securely expose your environment (applications, data, and resources) to vendors, distributors, and other organizations.

Workforce Identity & Access Management: EIAM
Provide simplified, secure access to internal systems to boost productivity and reduce risk.
.webp?width=582&height=793&name=7coILdZQ%201-2%20(1).webp)
Check how we can design a human centered security for your company.
What is the best IAM for you?
Take our 30-second quiz to find out which IAM is best for your business.
See more success stories of our
clients

The new standard of secure customer login
No passwords. Less friction. Higher conversion rates from the first visit to checkout.

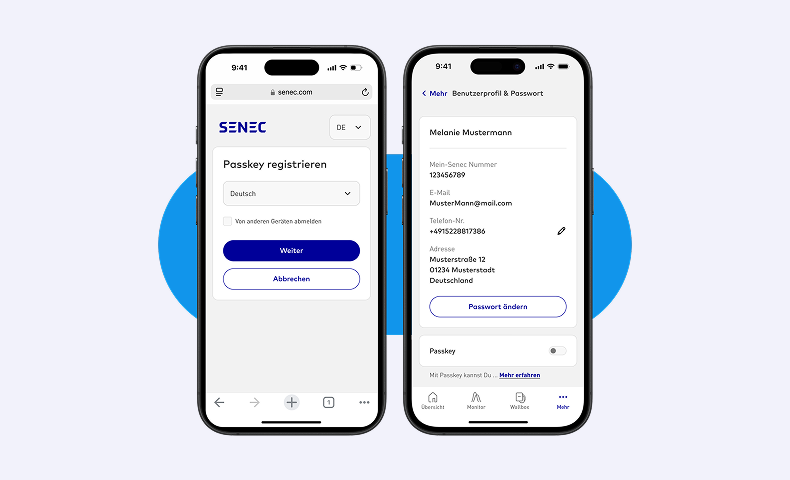
Passkeys
Passkeys replace passwords with device-based cryptographic authentication. With a simple fingerprint or facial scan, the device securely signs a server challenge using a private key - no passwords, resets, or phishing. The result? Checkout takes seconds, password fatigue disappears, and support workload drops. Friction vanishes, boosting conversion rates as more customers complete their purchases. Passkeys work across all major platforms, including iOS 16+, Android, Chrome, Safari, and Edge. Built on FIDO2 cryptography, they’re inherently phishing-resistant.
SSO – Single Sign-on
Customers log in once at your main store and are recognized across your entire ecosystem - mobile app, loyalty dashboard, and community forum. One authentication. One unified customer record. Built on standards (OIDC for modern apps, SAML for legacy systems), a single session provides seamless access: login once, access everywhere; logout once, signed out everywhere. Unified data provides a comprehensive view of customer behavior, revealing patterns that fragmented records overlook. SSO reduces friction, which boosts engagement, repeat purchases, and retention.


2FA/MFA
Account takeover fraud results in lost customer trust, damages brand reputation, and increases operational costs through investigations and support overhead. Without MFA, attackers can use stolen credentials to succeed. However, requiring MFA for every login can frustrate customers and drive them away. Adaptive MFA solves this problem. It scores each login in real time by looking at the device used, its location, the time of day, and the browser used. Low-risk logins skip MFA, while high-risk logins trigger it. The result? Fraud is blocked, legitimate users experience no friction, conversions increase, chargebacks decrease, and customer trust grows.
Our IAM delivery framework behind
the results
We follow a proven process that ensures a thorough diagnosis and accurate solutions.
What we do:
- Human-centered risk assessment: Analyze user behaviors, real-world contexts, and day-to-day workflows to identify friction points resulting in security workarounds or unsafe practices.
- Full review of your login experience: screens, redirects, MFA, account recovery, error handling, password fatigue, and support workload.
- Technical and security assessment: OAuth2 / OpenID Connect / SAML usage, password/token/session storage, rate limiting, brute-force protection, 2FA/MFA.
- Compliance check: industry and regulatory standards (GDPR, SOC 2, PSD2) and internal policies.
Impact: Gain a clear picture of your current state, a prioritized list of risks, and a roadmap for improved UX, security, and cost efficiency.
What we do:
- Design target IAM architecture: cloud or custom solution tailored to business and regulatory requirements.
- Implement and configure identity servers: realms, clients, roles, access policies, OAuth2 / OpenID Connect / SAML 2.0, SSO, session lifetimes, refresh tokens.
- Enable passkeys / WebAuthn / FIDO2: passwordless login or second-factor authentication for iOS, Android, Chrome, Safari, Edge.
- Integrate with existing systems: LDAP / Active Directory / Azure AD, user federation, attribute mapping, logging, and audit-ready reporting.
Impact: A modern, scalable IAM backbone that reduces security risk, simplifies integrations, and makes future features like SSO
and passwordless login easy to adopt.
What we do:
- Integrate the new authentication model into web apps (SPA/MPA) and mobile apps (iOS/Android, native or cross-platform).
- Use native standards: WebAuthn / passkeys via JavaScript, iOS system passkeys (16/17+), Android Credential Manager / passkeys.
- Smooth UX: passkeys as a convenient option, with solid fallbacks like password or magic links.
- Easy integration: ready-to-use UI components, sequence diagrams, sample requests/responses, and support for code review and production rollout.
Impact: Frictionless login users adopt, fewer failed logins and support tickets, and a faster, safer authentication experience across all platforms.
What we do:
- Design consistency validation: Ensure that the Low-Level Design (LLD) and code implementation strictly adhere to the High-Level Design (HLD) security architecture.
- Code and logic review: Conduct an in-depth review of edge cases, data validation and regulatory compliance to prevent design drift and embed security into the software.
Impact: A certified, resilient system in which the implemented code aligns with the architectural vision, thereby minimizing technical debt
and behavioral risks.
We integrate with the platforms you already use




Check how we approach building Human-Centered Identity Access Management
Phishing attacks are becoming increasingly sophisticated and often bypass traditional security measures. In one case, a senior manager received a highly targeted phishing email that mimicked an internal message. Rather than blaming the user, the organization's security-by-design approach prevented the attack. This approach embeds protections into architecture, workflows, and identity management. It shows how proactive security can stop even the most advanced threats.


Frequently
asked questions
What is Identity and Access Management (IAM), and why is it important?
IAM ensures that the right people have access to the right systems at the right time. It centralises authentication and authorisation across all applications, reducing security risks and simplifying audits while improving user experience and ensuring compliance with regulations such as GDPR, CCPA and PSD2.
How do CIAM, PIAM, and WIAM differ?
Customer Identity and Access Management manages millions of customer identities, providing a smooth and secure login experience, ensuring regulatory compliance, and enabling personalization and trust. Partner IAM provides external partners with controlled access to your applications and data while supporting single sign-on and precise access permissions. Employee IAM simplifies internal access, automates onboarding and offboarding, and strengthens security across all internal systems.
What security features are included in Unravel’s IAM solutions?
Our IAM solutions provide multi-factor and adaptive authentication, passwordless login with passkeys, single sign-on across web and mobile applications, granular role-based access control, delegated administration for partners and teams, account takeover prevention, and instant offboarding to protect your users and systems from unauthorized access.
How do passkeys improve user experience and security?
Can IAM scale for millions of users?
How does Unravel’s IAM ensure regulatory compliance?
Will IAM integrate with my existing systems?
What is Unravel’s process for implementing IAM?
Credential Theft: 71 % of cyberattacks involve the use of stolen credentials.
The years 2025–2026 represent the tipping point where Passkeys (FIDO2/WebAuthn) become the enterprise standard, effectively moving traditional passwords to "legacy" status.
Non-human identities (NHIs)—such as bots, service accounts, and AI agents—already outnumber human accounts in most corporate environments, often by a ratio of 45:1
Nearly 60% of enterprises have reported incidents where AI-generated voices or videos (Deepfakes) were used to attempt to bypass biometric or visual identity verification.
Cybercrime is projected to cost the global economy $23 trillion annually by 2027—a staggering 175% increase from 2022 levels.
By 2030, an estimated 6.2 billion people will be using digital identity apps, signaling a worldwide shift toward decentralized and mobile-first identity models.
By 2028, 50% of organizations will adopt Zero-Trust data governance specifically to combat the surge of unverified, AI-generated data entering their systems.